Personal Information: Definitions and Examples
Updated: March 2026
Personal information, also called personal data, is any information that relates to an identified or identifiable living person. Under the General Data Protection Regulation (GDPR), this includes not just names and addresses, but also IP addresses, device identifiers, and combinations of data that together single out an individual.
This guide covers:
• Your organisation’s obligations and the consequences of non-compliance
• The legal definition of personal information under GDPR and UK GDPR
• Practical examples across every data category
• Special category (sensitive) data and its stricter legal requirements
• Anonymisation vs. pseudonymisation: what does the difference mean in practice
What counts as personal information under GDPR?
Personal information under GDPR means any information relating to an identified or identifiable natural person. A person is identifiable if they can be directly or indirectly identified by name, identification number, location data, online identifier, or any combination of factors specific to their physical, physiological, genetic, mental, economic, cultural, or social identity.
This definition comes from Article 4(1) of the General Data Protection Regulation (EU) 2016/679, which has applied across the European Union since 25 May 2018. The UK GDPR, incorporated into UK law by the Data Protection Act 2018, retains the same definition.
The deliberate breadth of this definition reflects the regulation’s intent: to protect individuals in an era where identity can be established through data points that, a decade ago, were considered anonymous. The Information Commissioner’s Office (ICO) clarifies in its guidance that personal data includes information that can indirectly identify a person, even if the identifying link requires additional steps or a third-party dataset.
“The term ‘personal data’ is the entry point to the GDPR. It determines whether the GDPR applies to a particular processing activity.”
European Data Protection Board (EDPB), Guidelines on the concepts of controller and processor, 07/2020
Three questions to determine whether data is personal information:
1. Can this data directly identify a living person?
2. Could this data, combined with other reasonably available information, identify a person?
3. Could someone with reasonable means use this data to single out an individual?
If the answer to any of these is yes, the data is personal information under GDPR, and the full weight of the regulation applies.
What are the most common examples of personal information?
The most common examples of personal information include names, email addresses, phone numbers, postal addresses, and dates of birth. As of 2026, the category also extends to digital identifiers (IP addresses, cookies, device IDs), financial records, biometric data, and behavioural profiles, all of which are explicitly covered by GDPR.
Basic identifying information
The most straightforward category of personal data includes:
• Full name
• Physical and mailing address
• Phone number (mobile or landline)
• Email address
• Date of birth
A single item from this list may not be sufficient to identify a specific person; a common surname alone, for example, cannot. But the combination of a name, address, and date of birth can almost always be used, which is why the ICO advises treating combinations of seemingly innocuous data points with the same care as direct identifiers. According to ICO guidance, “you need to consider whether the combination of the items of data could create a more serious impact than the individual items would on their own.”
Official identification numbers
Identification numbers are among the most sensitive forms of personal data because they are designed to be unique to one individual. As of 2025, identity fraud using stolen identification numbers costs the UK economy an estimated £3.5 billion per year (Cifas, Fraud Landscape Report 2024). Examples subject to GDPR protection include:
• Passport numbers
• National Insurance numbers (UK) or Social Security numbers (US)
• Driver’s licence numbers
• Customer or account numbers
• Tax identification numbers
• NHS numbers (UK) or national health identifiers
The European Data Protection Board (EDPB) has confirmed in its guidelines that identification numbers require heightened protection given their potential for misuse in identity fraud and financial crime.
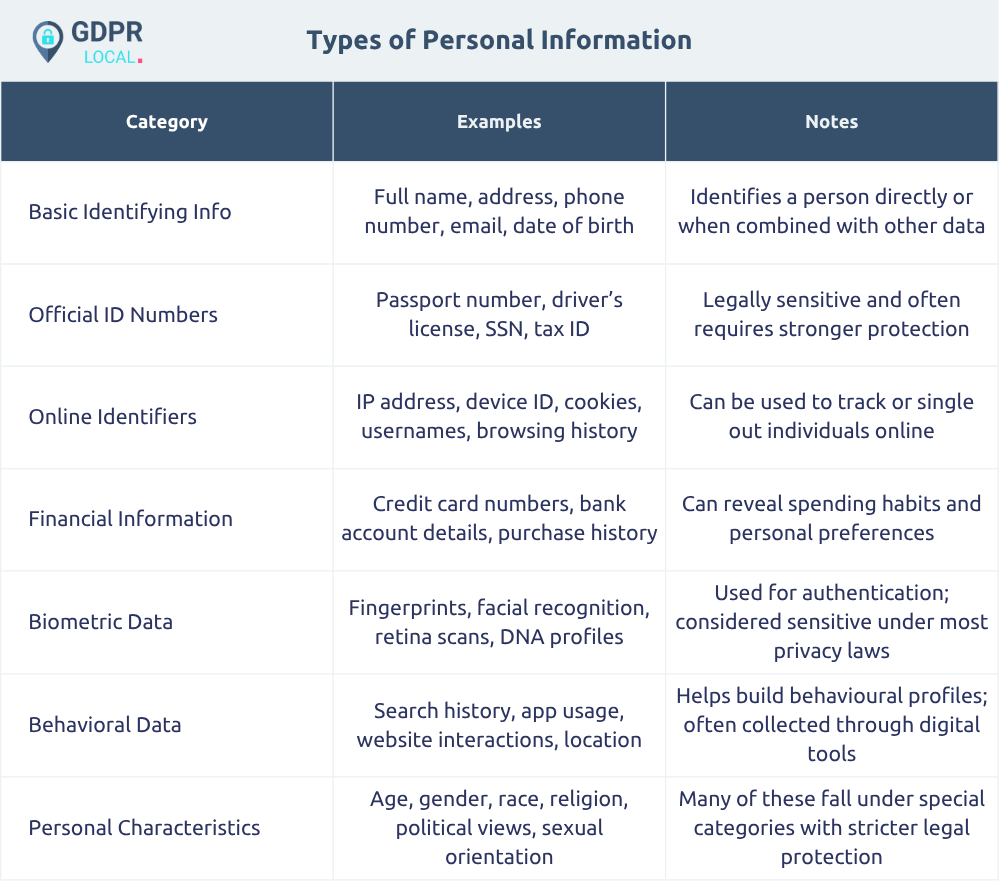
Are IP addresses personal data under GDPR?
Yes. IP addresses are personal data under GDPR. The Court of Justice of the European Union (CJEU) confirmed this in its 2016 ruling in Breyer v. Bundesrepublik Deutschland (Case C-582/14), finding that a dynamic IP address constitutes personal data for any party that has the legal means to identify the person behind it. This ruling remains binding case law in the EU as of 2026.
Online identifiers that qualify as personal data include:
• IPv4 and IPv6 addresses (both static and dynamic)
• Device IDs and hardware identifiers
• Browser cookies and tracking pixels
• Advertising identifiers (Google GAID, Apple IDFA)
• Login credentials and usernames
• Internet browsing history and search queries
The EDPB’s guidelines on cookies and tracking technologies (updated in 2023) reinforce that any identifier capable of singling out a user, even without a name, constitutes personal data under Article 4(1) of the GDPR. In practical terms, this means website analytics tools, advertising platforms, and server log files all generate personal data as a matter of course.
Commercial and financial information
Financial data carries dual risk: it is both personally identifying and commercially sensitive. GDPR-covered financial personal data includes credit and debit card details, bank account and sort code numbers, purchase histories and transaction records, and billing information. This category sits at the intersection of GDPR and sector-specific regulations, including the Payment Services Directive 2 (PSD2) and FCA Consumer Duty rules in the UK.
Behavioural and location data
One of the most significant expansions in what constitutes personal data under modern regulation is the inclusion of behavioural and location information, including app usage patterns, precise GPS coordinates, movement history, and purchase preferences, used for profiling. According to ICO guidance on online tracking, behavioural profiles built from these data points are “clearly personal data, regardless of whether a name is attached.”
What is sensitive personal data?
Sensitive personal data, also known as “special category data” under GDPR Article 9, is a subset of personal information that carries a higher risk of discrimination or harm if misused. It covers health data, biometric data, racial origin, political opinions, and religious beliefs. Processing it requires explicit consent or another specific legal condition, and it is subject to stricter security obligations than ordinary personal data.
Article 9 GDPR identifies nine categories of special category data:
1. Racial or ethnic origin
2. Political opinions
3. Religious or philosophical beliefs
4. Trade union membership
5. Genetic data (unique to a natural person’s biological characteristics)
6. Biometric data processed to uniquely identify a natural person (fingerprints, facial recognition templates, voiceprints)
7. Health data (physical or mental health status, medical records, prescriptions)
8. Sex life or sexual orientation
9. Criminal conviction and offence data (Article 10 GDPR, separate legal regime)
The harm that can result from exposure to this data is well documented. The ICO’s 2024 report on data breaches found that healthcare data is the most commonly breached special category type in the UK, and notes that unauthorised disclosure has led to employment discrimination, insurance rejections, and significant personal distress in recorded cases.
According to the GDPR Enforcement Tracker (CMS Law, updated 2025), insufficient security of sensitive personal data is among the three most frequently cited violation types in GDPR enforcement actions across EU member states.
What legal conditions allow processing of special category data?
Standard personal data can be processed on one of six legal bases under Article 6 GDPR. Special category data requires one of those Article 6 bases plus one of ten additional conditions from Article 9(2), the most commonly used in commercial contexts being:
• Explicit consent, a clear, affirmative statement (not pre-ticked boxes, not implied agreement)
• Employment obligations, e.g., occupational health assessments
• Medical or occupational health purposes, by health professionals under confidentiality obligations
• Substantial public interest requires a suitable policy document in the UK
• Legal claims, where processing is necessary for legal proceedings
“Explicit consent” under Article 9 sets a higher bar than standard consent: it requires a clear, written statement by the data subject specifically referencing the sensitive data category. Bundled consent clauses buried in terms and conditions do not meet this standard.
What is the difference between anonymisation and pseudonymisation?
Anonymisation permanently removes the ability to re-identify an individual from a dataset, meaning it is no longer personal data and GDPR no longer applies. Pseudonymisation replaces direct identifiers with codes or tokens but keeps a link-back key, so the data remains personal data and all GDPR obligations continue to apply. Confusing the two is a common and costly compliance mistake.
What does genuine anonymisation require?
For data to be considered truly anonymised under GDPR Recital 26, the process must pass three tests set out by the Article 29 Working Party (now the EDPB) in Opinion 05/2014 on Anonymisation Techniques:
1. Singling out – Is it possible to isolate some or all records relating to an individual?
2. Linkability – Is it possible to link two records relating to the same person?
3. Inference – Is it possible to deduce a value for one attribute from the values of others?
If a dataset fails any one of these tests, it is not truly anonymised, and GDPR continues to apply. Research from the Nature Communications journal (2019) demonstrated that 99.98% of individuals in a “anonymised” mobility dataset could be re-identified using just four spatio-temporal data points, a finding that underscores how difficult genuine anonymisation is in practice.
How does pseudonymisation work in practice?
Pseudonymisation replaces identifiers, names, email addresses, and national IDs with a code or token, while the key to reverse the process is stored separately and secured. Common techniques include:
• Replacing names with random reference numbers
• Data masking (replacing characters in sensitive fields with placeholder characters)
• Tokenisation (replacing payment card numbers with secure tokens)
• Encryption with separately stored decryption keys
Pseudonymised data is explicitly recognised in GDPR Article 89 as a useful security measure that “can reduce the risks to the data subjects and help controllers and processors meet their data protection obligations.” However, it remains personal data and must be protected accordingly.
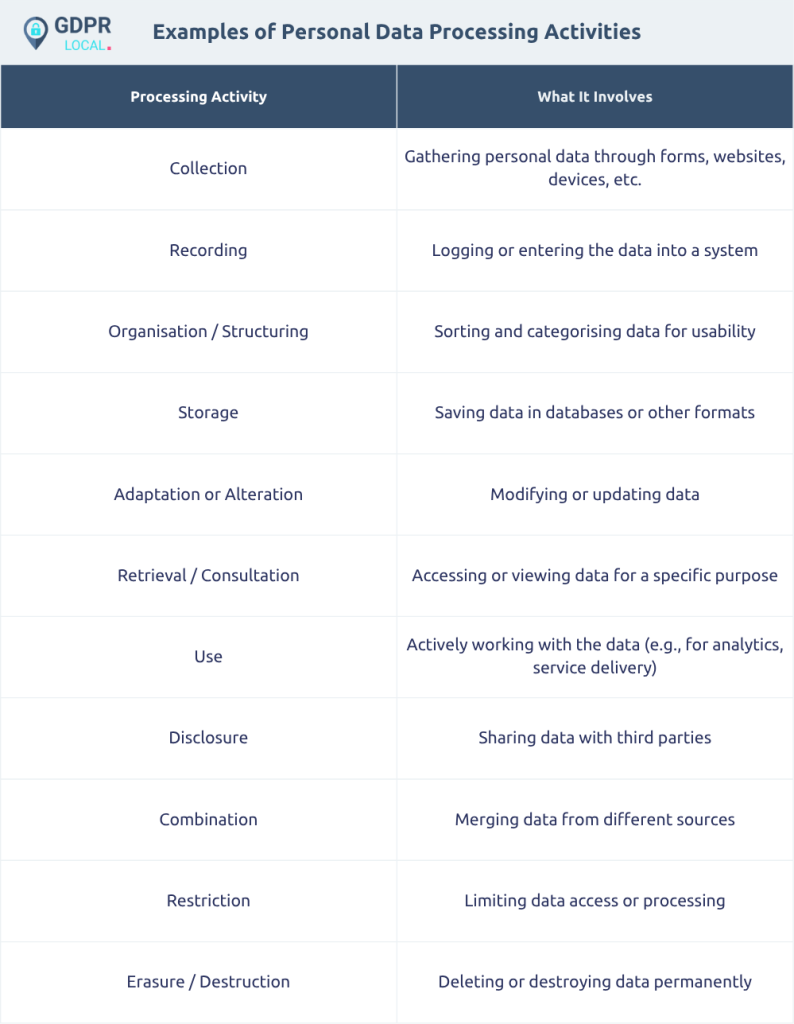
What are the six GDPR principles every organisation must follow?
Under Article 5 GDPR, organisations processing personal data must follow six binding principles: lawfulness/fairness/transparency; purpose limitation; data minimisation; accuracy; storage limitation; and integrity/confidentiality. These are legal obligations, not guidelines, and failure to comply with any one of them constitutes a GDPR violation in itself.
1. Lawfulness, fairness, and transparency
Every processing activity requires a valid legal basis under Article 6. Processing must be fair, not used against individuals’ reasonable expectations, and individuals must be informed through clear, accessible privacy notices before or at the point of data collection.
2. Purpose limitation
Data collected for one specific purpose cannot be silently repurposed. Email addresses collected for transactional communications cannot be redirected to marketing campaigns without a separate, documented legal basis. The ICO’s purpose limitation guidance confirms that “further processing must be compatible with the original purpose.”
3. Data minimisation
Only the personal data strictly necessary for the stated purpose should be collected. As of 2024-2025, data minimisation violations have featured in several high-profile enforcement actions, including fines imposed on mobile applications that collect excessive device permissions unrelated to their stated functions.
4. Accuracy
Personal data must be kept accurate and up to date. Individuals have the right to rectification under Article 16 of the GDPR, and organisations must have documented processes to act on these requests within one calendar month.
5. Storage limitation
Personal data must not be kept for longer than is necessary for its stated purpose. This requires documented retention schedules for every data category, with defined deletion or anonymisation procedures and dates.
6. Integrity and confidentiality (security)
Under Article 32 GDPR, organisations must implement technical and organisational security measures appropriate to the risk. The standard is not absolute security; it is security appropriate to the nature, scope, and sensitivity of the data being processed.
What are the consequences of failing to protect personal information?
Organisations that fail to protect personal data face GDPR fines of up to €20 million or 4% of annual global turnover, whichever is higher. As of early 2026, total GDPR fines issued by EU and UK supervisory authorities have exceeded €5 billion, with single penalties reaching into the hundreds of millions of euros against major platforms.
Non-financial consequences are often equally damaging:
• Enforcement orders: supervisory authorities can order organisations to stop processing, delete data, or halt cross-border data transfers
• Reputational damage: high-profile breaches consistently erode customer trust and brand value, research shows organisations reporting the largest breaches lose an average of 5-7% of their share price in the immediate aftermath
• Civil litigation: under Article 82 GDPR, data subjects can claim compensation for both material and non-material damage
• Business disruption: regulatory investigations can last months or years, consuming significant executive, legal, and operational resources
Notable enforcement examples (source: GDPR Enforcement Tracker):
• Meta Platforms Ireland – €1.2 billion (DPC, May 2023) for unlawful EU-US data transfers
• Amazon Europe Core – €746 million (CNPD Luxembourg, 2021) for advertising consent failures
• WhatsApp Ireland – €225 million (DPC, 2021) for transparency and data subject rights failures

What are the best practices for protecting personal information in 2026?
Organisations should implement data protection by design and by default, integrating privacy into systems from the outset rather than retrofitting it. The most effective protection combines technical controls (encryption, access controls, pseudonymisation) with organisational measures (staff training, clear retention policies, documented incident response, and regular audits). As of 2025, Cisco’s Privacy Benchmark Study found that organisations investing in strong privacy practices achieved an average benefit of $2.70 for every $1 invested.
Technical safeguards
• Encryption at rest and in transit: TLS 1.2+ for data in transit; AES-256 for stored personal data is the current recommended standard.
• Role-based access control (RBAC): only authorised personnel have access to personal data, on a need-to-know basis
• Pseudonymisation: apply tokenisation or data masking to reduce exposure in the event of a breach
• Secure deletion: documented deletion procedures ensure personal data is fully purged when retention periods expire
• Vulnerability management: regular patching schedules and penetration testing identify weaknesses before attackers do
Organisational measures
• Data Protection Impact Assessments (DPIAs): required under Article 35 GDPR for high-risk processing; best practice for any new system handling significant personal data
• Records of Processing Activities (RoPAs): a documented inventory of all processing activities (required for organisations with 250+ employees or processing special category data)
• Staff training: the ICO consistently identifies human error as a leading cause of personal data breaches; regular, role-specific training meaningfully reduces this risk
• Incident response plans: tested procedures for detecting, containing, and notifying breaches within the 72-hour reporting window under Article 33 GDPR
• Vendor due diligence: Data Processing Agreements (DPAs) must be in place with all processors, with documented security assessments before onboarding
Frequently Asked Questions
Is a person’s name alone personal data?
A person’s name is personal data when it identifies a specific individual. Very common names may require additional data points, such as employer or address, to identify a specific person. Combinations of data that together identify someone are covered by the GDPR, even if no single element is sufficient on its own.
Are email addresses personal data under GDPR?
Yes. An email address containing a person’s name ([email protected]) directly identifies them. Even non-name email addresses (e.g., [email protected]) are personal data under GDPR because they are linked to an identifiable account. This applies whether the email address belongs to a consumer or a named professional at a business.
Is CCTV footage personal data?
Yes. CCTV footage that captures images of identifiable individuals is personal data under GDPR. Organisations operating CCTV must display clear notices, have a lawful basis for processing, set documented retention periods, and respond to Subject Access Requests from individuals who appear in the footage. The ICO’s CCTV guidance provides detailed obligations for operators.
Does GDPR apply to employee personal data?
Yes. Employee personal data, including payroll records, performance reviews, disciplinary files, absence records, and health information, is fully subject to GDPR. The processing of employee data typically relies on contractual necessity, legal obligation, and (for sensitive health data) employment law obligations under Article 9(2)(b).
Do I need consent to collect and process personal data?
Not necessarily. Consent is one of six legal bases under Article 6 GDPR. Many processing activities are lawful on other bases, for example, processing necessary to perform a contract, comply with a legal obligation, or pursue legitimate interests. The ICO advises that consent should be relied upon only when no other basis is available, as it can be withdrawn at any time.
What is a Subject Access Request (SAR)?
A Subject Access Request (SAR) is an individual’s right under Article 15. Organisations must respond within one calendar month (extendable to three months for complex cases) and generally cannot charge a fee. As of 2025, SARs are the most commonly exercised data subject rights in the UK; the ICO reported a significant year-on-year rise in SAR complaints.
What is the difference between a data controller and a data processor?
A data controller is the organisation that determines the purposes and means of processing personal data. A data processor processes data on behalf of the controller, for example, a cloud hosting provider, payroll bureau, or email marketing platform. Controllers bear the primary compliance responsibility, but processors have direct obligations under Articles 28-29 of the GDPR and can be fined independently.
What is a personal data breach, and when must it be reported?
A personal data breach is any security incident leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to personal data. Under Article 33 GDPR, notifiable breaches must be reported to the relevant supervisory authority (ICO in the UK, the relevant national DPA in the EU) within 72 hours of becoming aware of the breach. Breaches unlikely to pose a risk to individuals do not require notification to supervisory authorities but must be documented internally.
How long can organisations keep personal data?
GDPR does not specify fixed retention periods for most data types. Organisations must determine and document appropriate periods based on the purpose of the collection, any statutory minimum or maximum periods, and a balance between the organisation’s interests and individuals’ rights. Data must be deleted or anonymised when the retention period expires.
Does GDPR apply to businesses outside the EU?
Yes, in many cases. Article 3(2) GDPR applies to organisations outside the EU when they offer goods or services to individuals in the EU, or monitor the behaviour of individuals in the EU (e.g., through website analytics or behavioural advertising). These organisations must typically designate an EU Representative under Article 27 GDPR. GDPRLocal’s Article 27 Representative service supports non-EU organisations in meeting this obligation.
What is the right to erasure (“right to be forgotten”)?
The right to erasure under Article 17 GDPR allows individuals to request deletion of their personal data in specific circumstances, for example, where consent is withdrawn, the data is no longer necessary for its original purpose, or processing was unlawful. This right is not absolute: it is subject to exemptions, including legal obligations, public-interest tasks, and freedom of expression.
Are photographs of employees’ personal data?
Yes. Photographs that clearly identify a living person are personal data under GDPR. Headshots in staff directories, images from team events, and any photo that can be linked to an identifiable individual are covered. Biometric templates derived from photographs, such as facial recognition data, fall under special category data and require explicit consent or another Article 9(2) condition.
What is a Data Processing Agreement, and when is it needed?
A Data Processing Agreement (DPA) is a contract required under Article 28 of the GDPR between a controller and any processor it engages. It must set out the subject matter, duration, nature, and purpose of the processing; the type of personal data involved; the processor’s security obligations; and the rights and obligations of both parties. Operating without a DPA in place is itself a GDPR violation.
What is a Data Protection Officer, and does my organisation need one?
A Data Protection Officer (DPO) is a designated individual responsible for overseeing data protection compliance. Article 37 GDPR mandates a DPO for public authorities and bodies; organisations whose core activities require large-scale, systematic monitoring of individuals; and organisations that process special category data at scale. Even where not legally mandatory, the ICO recommends appointing a DPO or a similar privacy lead. GDPRLocal provides outsourced DPO services for organisations that need qualified oversight without an in-house resource.
Conclusion
The definition of personal information continues to expand as digital technologies evolve. What once seemed anonymous, an IP address, a device ID, a browsing pattern, is now firmly within the scope of data protection law. As of 2026, organisations face stricter enforcement, larger fines, and more empowered data subjects than at any point since GDPR came into force.
The foundations have not changed: understand what personal data you hold, collect only what you need, protect it appropriately, and be transparent with individuals about how it is used. What has changed is the technical sophistication required to meet those obligations at scale and the regulatory willingness to impose serious consequences when organisations fall short.
If you need help reviewing your data inventory, implementing appropriate safeguards, or responding to data subject requests, the GDPRLocal compliance team can help. Contact us here, or sign up for free to get started.
Note: This content is created with AI assistance.

About the Author
Ana Mishova
Sales and Business Development Consultant — GDPRLocal
Ana focuses on helping organisations understand their compliance obligations and find the right data protection solutions. At GDPRLocal she works closely with businesses of all sizes, making GDPR and privacy compliance clear, practical, and accessible.